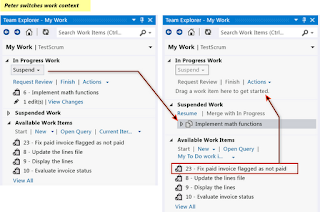
Visual Studio 2012 New Feature MY Work
Wednesday, September 26, 2012
Posted by Usama Wahab Khan at 10:45 AM 2 comments
Labels: visual Studio 2012
The Visual Guide for Building Team Foundation Server 2012 Environments
Tuesday, September 25, 2012
Watch the Videos
This Guide comes with 38 videos that explain all scenarios in a step-by-step manner.Parts
Chapters
Part 1- Introduction & Overview
- Chapter 1: Introduction
- Chapter 2: Architecture & System Requirements
Part 2 - Creating & Preparing the Required Infrastructure
- Chapter 3: Creating & Preparing the Domain Controller
- Chapter 4: Creating & Preparing the TFS Infrastructure Physical Machine (Hyper-V Host)
- Chapter 5: Creating & Preparing the Team Foundation Server Virtual Machine
Part 3- Installing and Configuring Team Foundation Server Pre-requisites
- Chapter 6: Installing & Configuring SQL Server 2012
- Chapter 7: Installing & Configuring SharePoint Server 2010
- Chapter 8: Configuring SharePoint Server 2010 for Dashboard Compatibility
Part Part 4- Installing and Configuring Team Foundation Server
- Chapter 9: Installing & Configuring Team Foundation Server 2012
- Chapter 10: Configuring the Team Build Service
- Chapter 11: Configuring the Enterprise Application Definition
Appendices
- A. Creating Local Service Accounts and Groups for Windows Server 2012
- B. Installing Hyper-V Role on Windows Server 2008 R2
- C. Adding .NET 3.5 Framework feature for Windows Server 2008 R2
- D. Configuring SQL Server 2012 Analysis Services Port
- E. Configuring SQL Server 2012 Database Engine Port
- F. SQL Server 2012 Installation Verification
- G. SharePoint Server 2010 SP1 Installation Verification
- H. Team Foundation Server 2012 Installation & Configuration Verification
Videos
- 3.1 Installing Windows Server 2008 R2 SP1
- 3.2 Creating the Service Accounts and Groups
- 4.1 Installing Windows Server 2012
- 4.2 Adding the Hyper-V Role to Windows Server 2012
- 5.1 Creating the TFS Virtual Machine
- 5.2 Installing Windows Server 2012
- 5.3 Configuring the Local Policies
- 6.1 Adding .NET 3.5 Windows Feature
- 6.2 Installing SQL Server 2012
- 6.3 Configuring Analysis Services to Recover on Failure
- 7.1 Adding the Required Roles and Features
- 7.2 Emulating the Exit Code
- 7.3 Installing SharePoint 2010 Prerequisites
- 7.4 Installing SharePoint Server 2010
- 7.5 Configuring the Default Application Pool
- 7.6 Configuring SharePoint Server 2010
- 8.1 Configuring the Excel Services Application
- 8.2 Configuring the Secure Store Service Application
- 9.1: Installing Team Foundation Server 2012
- 9.2: Configuring Team Foundation Server 2012
- 10: Configuring the Team Build Service
- 11: Configuring the Enterprise Application Definition
- Appendix A: Creating Local Service Accounts and Groups for Windows Server 2012
- Appendix B: Adding the Hyper-V Role to Windows Server 2008 R2
- Appendix C: Adding .NET 3.5 Framework feature to Windows Server 2008 R2
- Appendix D: Configuring SQL Server 2012 Analysis Services Port
- Appendix E: Configuring SQL Server 2012 Database Engine Port
- Appendix F-1: Verifying SQL Server Reporting Services
- Appendix F-2: Verifying SQL Server Database Engine and SQL Server Analysis Services
- Appendix F-3: Verifying the Connection to SQL Server Instance (Database and Analysis Service)
- Appendix G-1: Verifying the Connection to the Web Applications
- Appendix G- 2: Verifying the Recommended Authentication Settings
- Appendix H-1: Installing Visual Studio 2012 Ultimate Edition
- Appendix H-2: Creating a New Team Project
- Appendix H-3 : Processing the Warehouse and the Analysis Databases
- Appendix H-4: Verifying the Excel Services Reporting
- Appendix H-5: Verifying the TFS Build Service
- Appendix G-3: Verifying SharePoint 2010 Dashboard Compatibility
Team
Reference
http://tfs2012visualguide.codeplex.com/
Posted by Usama Wahab Khan at 6:50 PM 0 comments
Labels: visual Studio 2012
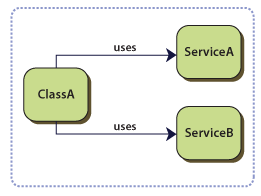
Most Important Design Patterns for SharePoint developer
Friday, September 21, 2012
A design pattern approach in SharePoint development is very important for standard and reusable Solution for most common problems in software development. A design pattern is not only for implementation of code. its solution template to solve real life Programmatic Problems. adopting design pattern approach to develop solution for SharePoint that allows you to formulate a high level Solutions that is independent of the implementation details.
Most Common Design Pattern for SharePoint Development.
- Model-View-Presenter (MVP)
- Repository
- Service Locator
- The Trusted Façade Pattern
- Duplicated code
- A higher potential for programming errors
- Weak typing of the business data
- Difficulty in centralizing data-related policies such as caching
- An inability to easily test the business logic in isolation from external dependencies
- You want to maximize the amount of code that can be tested with automation and to isolate the data layer to support unit testing.
- You access the data source from many locations and want to apply centrally managed, consistent access rules and logic.
- You want to implement and centralize a caching strategy for the data source.
- You want to improve the code's maintainability and readability by separating business logic from data or service access logic.
- You want to use business entities that are strongly typed so that you can identify problems at compile time instead of at run time.
- You want to associate a behavior with the related data. For example, you want to calculate fields or enforce complex relationships or business rules between the data elements within an entity.
- You want to apply a domain model to simplify complex business logic.
- The concrete implementation of the dependencies must be available at compile time.
- Your classes are difficult to test in isolation because they have a direct reference to their dependencies. This means that these dependencies cannot be replaced with stubs or mock objects.
- Your classes contain repetitive code for creating, locating, and managing their dependencies.
- The next section describes how to address these issues.
- You want to be able to test your classes in isolation, without the dependencies.
- You do not want the logic that locates and manages the dependencies to be in your classes.
- You want to divide your application into loosely coupled modules that can be independently developed, tested, versioned, and deployed.
- Authenticate external users of a SharePoint application that is located in a perimeter network. The SharePoint application uses a credential store that is also in the perimeter network.
- Authenticate the SharePoint application in a perimeter network to a Web service in the corporate network with credentials that are recognized in the corporate security domain.
- Ensure the confidentiality and integrity of messages that are exchanged between the SharePoint application and the Web service.
- Have a Web service in a corporate domain apply authorization rules that are based on the identity of the external user.
- Avoid creating additional credential stores to store passwords in the SharePoint application.
Posted by Usama Wahab Khan at 5:38 AM 7 comments
Labels: Design Patterns, Share Point, SharePoint 2013
Dev Saturday UAE – Pilot
Monday, September 17, 2012
Out Frist Great Effort with UAE DEV Community. Thanks to All member of Dev Saturday UAE. to make this event and community. Special thanks for All Student off Khalifa University and IEEE.
- Khalifa University’s IEEE Student Chapter, Abu Dhabi Campus.
- Dev Saturday UAE
Great Community UserGroup Startup with Oubai Abbasi Omar A. Rizk, Khalild,Ali.
http://devsaturdayuae.eventbrite.com/
FaceBook : Join US
https://www.facebook.com/groups/254601744660754/
Posted by Usama Wahab Khan at 9:25 AM 0 comments
Labels: Dev Saturday UAE, Usama wahab khana